EFT and ICAP
#25 TOP TIP for Globalscape EFT ServerCould DLP could have prevented the Morrisons data breach where a member of staff leaked personal data of over 100,000 employees? EFT Server uses ICAP Scanning to deliver Antivirus (AV) and Data Loss Prevention (DLP). This top tip provides a brief introduction and includes screenshots.
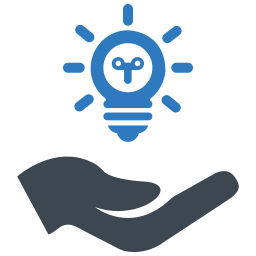
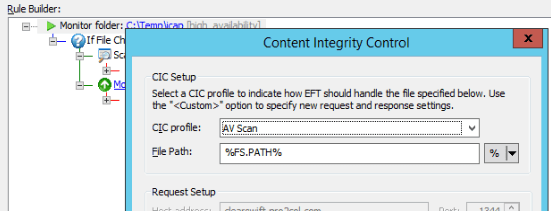
ICAP (Internet Content Adaption Protocol) delivers Antivirus (AV) and Data Loss Prevention (DLP) through an HTTP interface. EFT Enterprise supports connections to an ICAP Server using the Content Integrity Control (CIC) module. After version 7.4.7, which was released in May 2018, the CIC module now forms part of the Advanced Security Module (ASM).
ICAP servers accept requests in one of two ways. The primary way is in ‘Response’ mode. This simply replies to a file request with a Pass or Fail, usually as a numeric code. In this way the ICAP Scanner is acting as a checkpoint, approving files for processing or stopping them if they break rules defined by system administrators
In ‘Request’ mode, the ICAP server can pass more than the simple Pass / Fail message and can include additional information such as the name of the virus or the reason why the file has ‘failed’ the scan. Some of the more recent scanners can now also redact (clean up) a file and pass it back to EFT to be processed. This could be by removing any malicious content, or obfuscating data which is not allowed to be sent – eg: bank details – making it unintelligible. This latter option is useful to protect personal data leaving a network, making sure you comply with GDPR.
ICAP connections are configured as a server-wide profile and scans are usually executed as a part of an event rule.
Checking for incoming viruses
Incoming files are usually passed to an AV ICAP scanner to ensure they are ‘Clean’. This is often done as a ‘File Upload’ rule which passes any uploaded file to the ICAP Scanner. Caution should be taken with large files or slow scans as, due to the mechanics of the ‘File Upload’ Event, responses to uploading clients can be delayed for the duration of the scan. If the scan takes longer than the timeout for the uploading client, then it is possible the client will see the upload as unsuccessful and may retry. If this is the case, it is recommended to extend the timeout period on the client to allow for the extended processing time.
Checking outgoing files
As mentioned, Event Rules can also be used to check outbound files before they are allowed to leave the network – normally this would be a DLP check, but there may also be an AV scan too. When passing any files to ICAP, you may define and select from a number of profiles which will allow for different security rules to be applied in different scenarios. For example, you may code one set of rules for transfer to a bank, and a different set of rules for a shipping company. Using different rules may also help you address issues with larger files. ICAP scanners which support redaction can be used to change files which contain sensitive information. For example if a file contains credit card numbers, it could be redacted to replace the first 12 digits with Xs making the credit card number appear as “XXXX XXXX XXXX 1234”.
Supported solutions
AntiVirus ICAP scanners supported by EFT are
- Kaspersky
- Sophos
- Symantec
- Trend Micro
DLP ICAP scanners supported by EFT are:
- Symnatec
- Websense
- McAfee
- RSA
In addition to these, EFT should be able to communicate with any solution which uses the ICAP protocol. Pro2col have also tested Clearswift, which has AntiVirus and DLP capabilities built into a single solution.
If you are interested in finding out more about ICAP scanning with EFT, or would like support getting it up and running in your organisation, please get in touch.
EFT Modules