For more on PCI DSS requirements and how EFT can directly assist compliance, download the White Paper “Facilitating Enterprise PCI DSS Compliance”.
GLOBALSCAPE EFT PCI DSS COMPLIANCE
What is PCI DSS?
PCI DSS is the worldwide Payment Card Industry Data Security Standard that was set up to help businesses process card payments securely and reduce card fraud. It’s achieved through enforcing tight controls surrounding the storage, transmission and processing of cardholder data that businesses handle. PCI DSS is intended to protect sensitive cardholder data.

The Standard is updating to version 3.2
The update to the Data Security Standard was introduced in 2016 and has since been considered best practice (and unenforceable) in the industry. But it won’t remain optional for long. The deadline for 3.2 compliance is February 1st 2018.
If you’re still following PCI DSS 3.1 requirements, now is the time to ensure your organization will be compliant with 3.2. There are five changes on the horizon; three are mandatory for everyone. They include:
Multi-Factor Authentication (MFA)
Reporting Processes Updates
New PAN Storage Requirements.
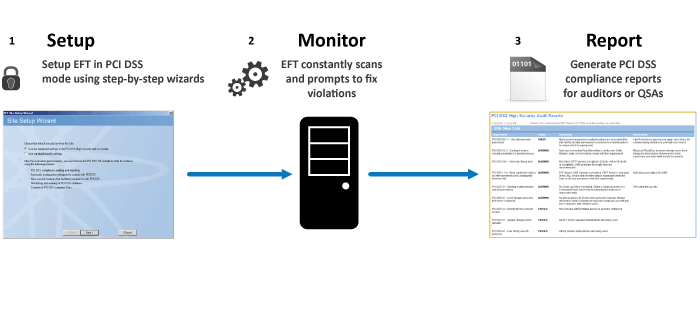
ACHIEVE AND MAINTAIN PCI DSS COMPLIANCE WITH EFT SERVER
Globalscape’s Enhanced File Transfer (EFT) High Security module (HSM) exceeds security practices mandated by the PCI DSS version 3, FIPS 140-2 Validation, HIPAA, Sarbanes-Oxley, and others for data transfer, access, and storage.
The HSM actively monitors PCI DSS by alerting on non-compliance, identifying the cause of non-compliance, allowing reverting of security controls, implementing mitigation/workaround techniques.
The High Security Module ensures:
- Data is stored and disposed of securely
- Account and password security policies adhere to industry standards
- Strong encryption ciphers and keys are used exclusively
- Violations are reported, compensating controls are applied, and changes are monitored and recorded
KEY FEATURES FOR PCI DSS
-
Protection of Data at Rest
Together the High Security module, EFT, and DMZ Gateway, help organisations comply with data storage requirements. By not storing data in the network’s demilitarised zone (DMZ), using repository encryption, and securely removing deleted data so that it cannot be reconstituted.
-
Protection of Data in Transit
With support for multiple security protocols and a built-in FIPS 140-2 validated cryptographic library, the HSM protects data in transit. By enforcing the use of secure protocols, strong ciphers and encryption keys, and maintaining password policies, data transfers strictly follow PCI DSS requirements.
-
Controlled Access to Data
The HSM enforces account access policy controls such as the automatic lock out of accounts after a set amount of incorrect login attempts and the removal of inactive accounts after a certain period of inactivity. Additional security controls can be set to expire passwords automatically on certain dates, and notifications such as emails and banners can be configured accordingly.
For user authentication, AD, NTLM, LDAP, or ODBC compatible database can be used, or EFT’s authentication manager.
-
Active Monitoring
The High Security module actively supports the PCI DSS by:
– Monitoring compliance
– Alerting on non-compliance
– Identifying the cause of non-compliance
– Allowing reverting of security controls
– Implementing mitigation/workaround techniques
– Providing reports for auditor sampling
The Auditing and Reporting Module (ARM) captures all server activity in a relational database.
-
Minimised Attack Vector
The HSM lets you leverage your existing Active Directory infrastructure for EFT administrator accounts, eliminating the need to create, maintain, and track standards compliance of built-in, administrator accounts typical of most MFT solutions.
-
Ongoing Globalscape PCI DSS Compliance
Securing sensitive company data requires continuous monitoring and validation of security policies and controls. Globalscape makes it easy for an administrator to create and maintain file-transfer services that meet or exceed these standards with a simple set-up wizard. Once enabled, the HSM is an ever-vigilant security tool that disallows low-security options, captures compensating controls, and generates reports for auditing the system’s compliance status.
