Achieving High Availability (HA)
for Globalscape EFT Server
Has your EFT Server grown from simply supporting tactical operations, to underpinning critical business processes? That means more transfers and a greater load on your server. System performance is impacted by high volumes of folders/files and spikes in traffic at busy times. But if EFT Server went down, would your business grind to a halt? The ‘active-active’ configuration, meaning multiple servers operating simultaneously, allows files to be transferred across more than one server. This load balancing eliminates down-time and keeps business processes running at busy times. Given the cost of failure, high availability (HA) is essential in today’s business environment. This article explores your options.
Many organisations now have more than one datacentre to ensure that mission critical systems are available nearly 100% of the time. Sending and receiving data using a Globalscape EFT Server frequently comes into the mission critical category but how do you achieve it? An obvious configuration would be to put a single node of a HA pair in each datacentre. Leaving out the networking issues of global and local traffic managers and load balancers, this would, on the face of it, would be the most logical configuration.
Both EFT Server and Mail Express support Active/Passive High Availability using windows clustering, but Globalscape will not support this configuration across datacentres. EFT Server also supports Active/Active High Availability where EFT acts as its own cluster manager. However, even with low network latency between the data centres, splitting an EFT Active/Active HA Pair across data centres is not a supported configuration either.
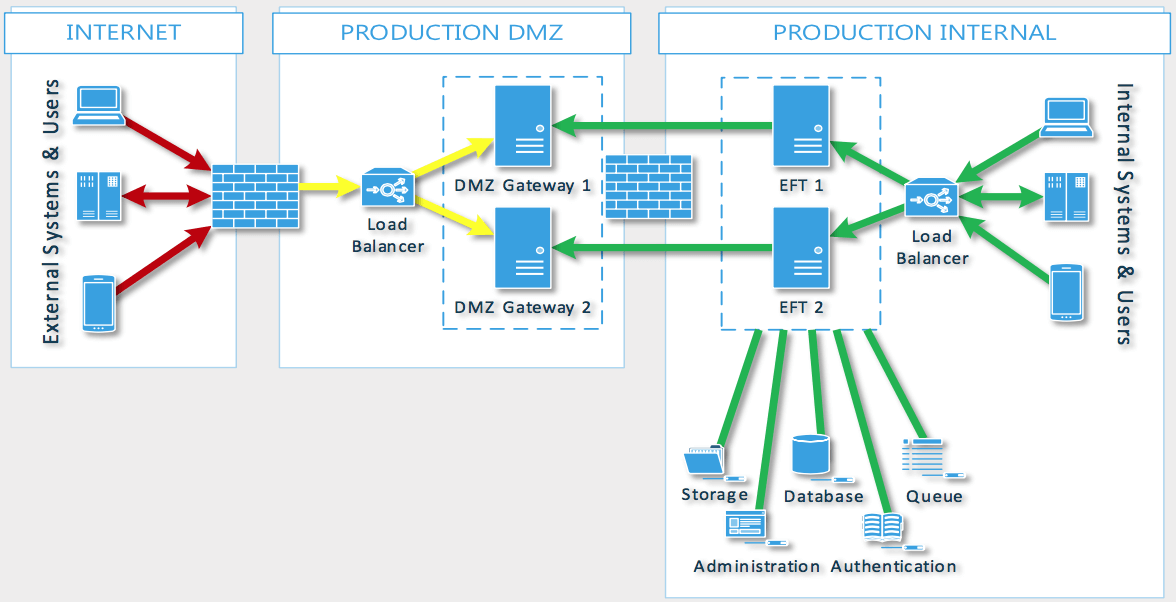
EFT Active-Active Configuration
The good news is that there are alternative ways to achieve the same functionality in a supported configuration.
If you are running in a virtualised environment, leveraging virtual technology such as VMware’s SRM, you’ll be able to automatically failover an EFT or MailExpress server to another datacentre. This allows an Active/Active configuration in the primary datacentre to give maximum resiliency and only in the case of the complete loss of the datacentre will the configuration be moved to the secondary datacentre.
This approach has a couple of advantages
- Server resilience during datacentre failure – while it is an extreme scenario, loss of a data centre can sometimes take a significant time to recover. During this time, having your system running in a HA mode will give you additional protection against system failure
- Gateways help connectivity – because of the way that EFT and MailExpress initiate the connections to DMZ Gateways, as long as the networking routes are in place, external partners will be able to use the same connection settings to transfer files within a few seconds of the servers coming up, irrespective of their location.
If you need to run EFT Server across more than one datacentre and SRM is not appropriate, there is a ‘sync tool’ application available that can be used to push configurations from a standalone EFT server to another EFT Server, which can be located on a remote datacentre. While it does not give a “true” Active/Active configuration, the sync tool, combined with shared storage, will allow the two EFT instances to appear the same. Another advantage of the EFT sync tool can also be that either EFT server can host sites, which are not needed to be replicated (such as test sites).
Why opt for HA in the cloud?
We are seeing increased demand for HA in the cloud in AWS, Azure and other cloud environments. There are several benefits to this set up:
-
LOAD BALANCING
Your EFT event rules can work on both servers – if a large file arriving on one EFT instance has a negative performance impact, rules (and logins) can continue to work on the alternate server.
There are various options for load balancing. Traffic can be directed according to rules you set on the load balancing device. As an example, you could select from one of the following:
Round robin – Connections are directed to each server alternately;
Least busy – Connections go to the server with the least number of active connections;
Weighted – One of the previous solutions, but without an ‘even’ spread (for example, one server receives 75% of traffic);
Dedicated purpose – All traffic for a specific purpose or protocol is directed to one node.
-
MIGRATION TO A CLOUD STRATEGY
Businesses are eager to reap the benefits of a cloud-based or hybrid infrastructure, such as increased speed of response and agility. Opting to host HA for your EFT Server in the cloud is an important step in your organisation’s cloud strategy without interrupting your current infrastructure.
-
EFFICIENT SOLUTION DESIGN
Many businesses have a hybrid infrastructure, combining on-premise and cloud-based applications. Set up a cloud-based EFT Server to support the cloud applications and keep your on-premise EFT solution only for on-premise exchanges. This more efficient solution design will reduce traffic. You will save money too by reducing the costs associated with moving data in or out of AWS, Azure or other cloud-based environment.
-
GEO CLUSTERING
Spreading your infrastructure across geographically dispersed sites – known as geo clustering – is important for business continuity. If your on-premise solution went down, your data would be routed through your cloud-based EFT Server, allowing business operations to continue uninterrupted.
If you wish to discuss how to achieve HA in your infrastructure, don’t hesitate to give the team here a call on 020 7118 9640.